EntryPoints¶
Opening Connections for Incoming Requests
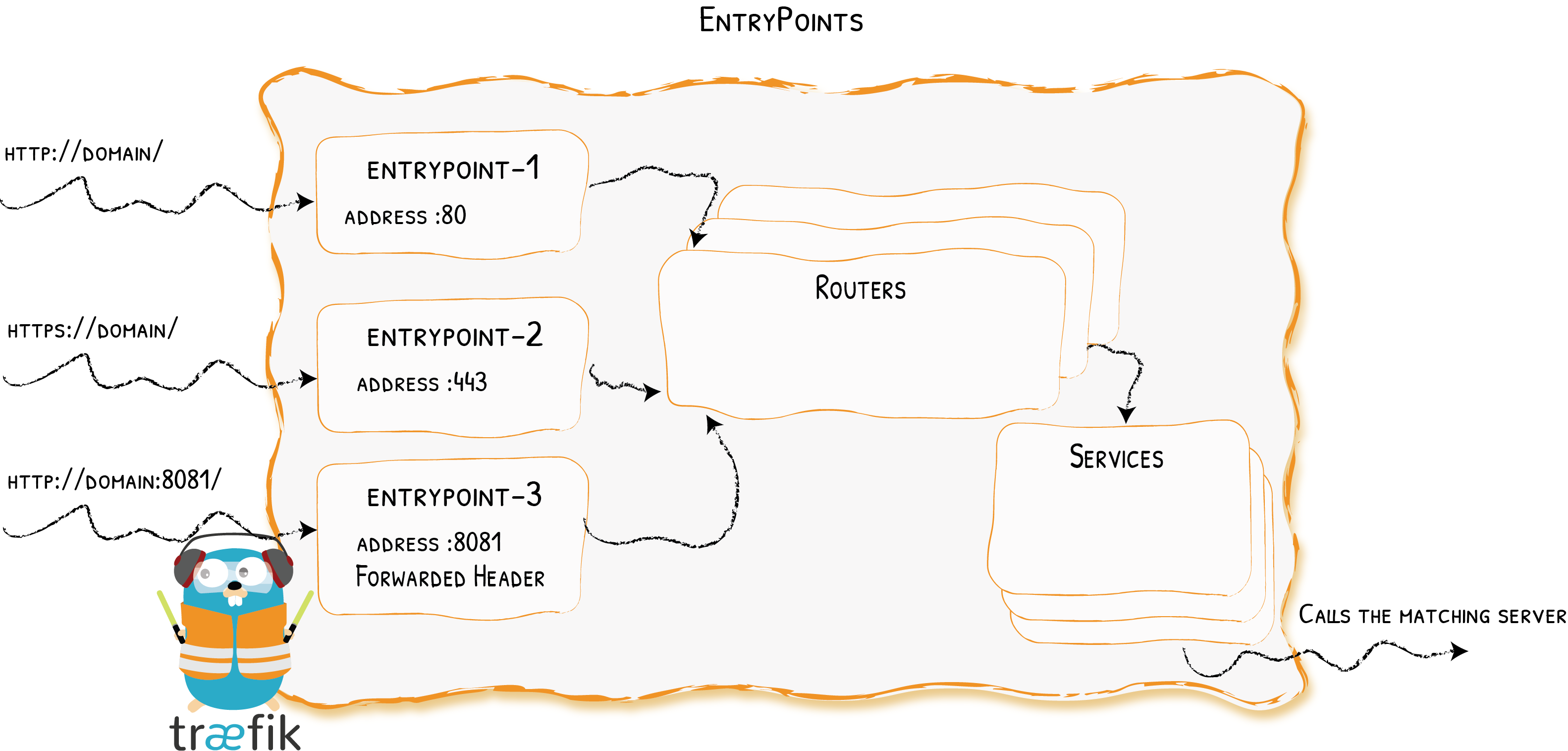
EntryPoints are the network entry points into Traefik. They define the port which will receive the packets, and whether to listen for TCP or UDP.
Configuration Examples¶
Port 80 only
## Static configuration
entryPoints:
web:
address: ":80"## Static configuration
[entryPoints]
[entryPoints.web]
address = ":80"## Static configuration
--entryPoints.web.address=:80We define an entrypoint called web that will listen on port 80.
Port 80 & 443
## Static configuration
entryPoints:
web:
address: ":80"
websecure:
address: ":443"## Static configuration
[entryPoints]
[entryPoints.web]
address = ":80"
[entryPoints.websecure]
address = ":443"## Static configuration
--entryPoints.web.address=:80
--entryPoints.websecure.address=:443- Two entrypoints are defined: one called
web, and the other calledwebsecure. weblistens on port80, andwebsecureon port443.
UDP on port 1704
## Static configuration
entryPoints:
streaming:
address: ":1704/udp"## Static configuration
[entryPoints]
[entryPoints.streaming]
address = ":1704/udp"## Static configuration
--entryPoints.streaming.address=:1704/udpConfiguration¶
General¶
EntryPoints are part of the static configuration. They can be defined by using a file (YAML or TOML) or CLI arguments.
See the complete reference for the list of available options
## Static configuration
entryPoints:
name:
address: ":8888" # same as ":8888/tcp"
http2:
maxConcurrentStreams: 42
http3:
advertisedPort: 8888
transport:
lifeCycle:
requestAcceptGraceTimeout: 42
graceTimeOut: 42
respondingTimeouts:
readTimeout: 42
writeTimeout: 42
idleTimeout: 42
proxyProtocol:
insecure: true
trustedIPs:
- "127.0.0.1"
- "192.168.0.1"
forwardedHeaders:
insecure: true
trustedIPs:
- "127.0.0.1"
- "192.168.0.1"## Static configuration
[entryPoints]
[entryPoints.name]
address = ":8888" # same as ":8888/tcp"
[entryPoints.name.http2]
maxConcurrentStreams = 42
[entryPoints.name.http3]
advertisedPort = 8888
[entryPoints.name.transport]
[entryPoints.name.transport.lifeCycle]
requestAcceptGraceTimeout = 42
graceTimeOut = 42
[entryPoints.name.transport.respondingTimeouts]
readTimeout = 42
writeTimeout = 42
idleTimeout = 42
[entryPoints.name.proxyProtocol]
insecure = true
trustedIPs = ["127.0.0.1", "192.168.0.1"]
[entryPoints.name.forwardedHeaders]
insecure = true
trustedIPs = ["127.0.0.1", "192.168.0.1"]## Static configuration
--entryPoints.name.address=:8888 # same as :8888/tcp
--entryPoints.name.http2.maxConcurrentStreams=42
--entryPoints.name.http3.advertisedport=8888
--entryPoints.name.transport.lifeCycle.requestAcceptGraceTimeout=42
--entryPoints.name.transport.lifeCycle.graceTimeOut=42
--entryPoints.name.transport.respondingTimeouts.readTimeout=42
--entryPoints.name.transport.respondingTimeouts.writeTimeout=42
--entryPoints.name.transport.respondingTimeouts.idleTimeout=42
--entryPoints.name.proxyProtocol.insecure=true
--entryPoints.name.proxyProtocol.trustedIPs=127.0.0.1,192.168.0.1
--entryPoints.name.forwardedHeaders.insecure=true
--entryPoints.name.forwardedHeaders.trustedIPs=127.0.0.1,192.168.0.1Address¶
The address defines the port, and optionally the hostname, on which to listen for incoming connections and packets. It also defines the protocol to use (TCP or UDP). If no protocol is specified, the default is TCP. The format is:
[host]:port[/tcp|/udp]If both TCP and UDP are wanted for the same port, two entryPoints definitions are needed, such as in the example below.
Both TCP and UDP on Port 3179
## Static configuration
entryPoints:
tcpep:
address: ":3179"
udpep:
address: ":3179/udp"## Static configuration
[entryPoints]
[entryPoints.tcpep]
address = ":3179"
[entryPoints.udpep]
address = ":3179/udp"## Static configuration
--entryPoints.tcpep.address=:3179
--entryPoints.udpep.address=:3179/udpListen on Specific IP Addresses Only
entryPoints:
specificIPv4:
address: "192.168.2.7:8888"
specificIPv6:
address: "[2001:db8::1]:8888"[entryPoints.specificIPv4]
address = "192.168.2.7:8888"
[entryPoints.specificIPv6]
address = "[2001:db8::1]:8888"--entryPoints.specificIPv4.address=192.168.2.7:8888
--entryPoints.specificIPv6.address=[2001:db8::1]:8888Full details for how to specify address can be found in net.Listen (and net.Dial) of the doc for go.
HTTP/2¶
maxConcurrentStreams¶
Optional, Default=250
maxConcurrentStreams specifies the number of concurrent streams per connection that each client is allowed to initiate.
The maxConcurrentStreams value must be greater than zero.
entryPoints:
foo:
http2:
maxConcurrentStreams: 250[entryPoints.foo]
[entryPoints.foo.http2]
maxConcurrentStreams = 250--entryPoints.name.http2.maxConcurrentStreams=250HTTP/3¶
http3¶
http3 enables HTTP/3 protocol on the entryPoint.
HTTP/3 requires a TCP entryPoint, as HTTP/3 always starts as a TCP connection that then gets upgraded to UDP.
In most scenarios, this entryPoint is the same as the one used for TLS traffic.
HTTP/3 uses UDP+TLS
As HTTP/3 uses UDP, you can't have a TCP entryPoint with HTTP/3 on the same port as a UDP entryPoint. Since HTTP/3 requires the use of TLS, only routers with TLS enabled will be usable with HTTP/3.
Enabling Experimental HTTP/3
As the HTTP/3 spec is still in draft, HTTP/3 support in Traefik is an experimental feature and needs to be activated in the experimental section of the static configuration.
experimental:
http3: true
entryPoints:
name:
http3: {}[experimental]
http3 = true
[entryPoints.name.http3]--experimental.http3=true
--entryPoints.name.http3advertisedPort¶
http3.advertisedPort defines which UDP port to advertise as the HTTP/3 authority.
It defaults to the entryPoint's address port.
It can be used to override the authority in the alt-svc header, for example if the public facing port is different from where Traefik is listening.
http3.advertisedPort
experimental:
http3: true
entryPoints:
name:
http3:
advertisedPort: 443[experimental]
http3 = true
[entryPoints.name.http3]
advertisedPort = 443--experimental.http3=true
--entryPoints.name.http3.advertisedport=443Forwarded Headers¶
You can configure Traefik to trust the forwarded headers information (X-Forwarded-*).
forwardedHeaders.trustedIPs
Trusting Forwarded Headers from specific IPs.
## Static configuration
entryPoints:
web:
address: ":80"
forwardedHeaders:
trustedIPs:
- "127.0.0.1/32"
- "192.168.1.7"## Static configuration
[entryPoints]
[entryPoints.web]
address = ":80"
[entryPoints.web.forwardedHeaders]
trustedIPs = ["127.0.0.1/32", "192.168.1.7"]## Static configuration
--entryPoints.web.address=:80
--entryPoints.web.forwardedHeaders.trustedIPs=127.0.0.1/32,192.168.1.7forwardedHeaders.insecure
Insecure Mode (Always Trusting Forwarded Headers).
## Static configuration
entryPoints:
web:
address: ":80"
forwardedHeaders:
insecure: true## Static configuration
[entryPoints]
[entryPoints.web]
address = ":80"
[entryPoints.web.forwardedHeaders]
insecure = true## Static configuration
--entryPoints.web.address=:80
--entryPoints.web.forwardedHeaders.insecureTransport¶
respondingTimeouts¶
respondingTimeouts are timeouts for incoming requests to the Traefik instance.
Setting them has no effect for UDP entryPoints.
transport.respondingTimeouts.readTimeout
Optional, Default=60s
readTimeout is the maximum duration for reading the entire request, including the body.
If zero, no timeout exists.
Can be provided in a format supported by time.ParseDuration or as raw values (digits).
If no units are provided, the value is parsed assuming seconds.
We strongly suggest to adapt this value accordingly to the your needs.
## Static configuration
entryPoints:
name:
address: ":8888"
transport:
respondingTimeouts:
readTimeout: 42## Static configuration
[entryPoints]
[entryPoints.name]
address = ":8888"
[entryPoints.name.transport]
[entryPoints.name.transport.respondingTimeouts]
readTimeout = 42## Static configuration
--entryPoints.name.address=:8888
--entryPoints.name.transport.respondingTimeouts.readTimeout=42transport.respondingTimeouts.writeTimeout
Optional, Default=0s
writeTimeout is the maximum duration before timing out writes of the response.
It covers the time from the end of the request header read to the end of the response write.
If zero, no timeout exists.
Can be provided in a format supported by time.ParseDuration or as raw values (digits).
If no units are provided, the value is parsed assuming seconds.
## Static configuration
entryPoints:
name:
address: ":8888"
transport:
respondingTimeouts:
writeTimeout: 42## Static configuration
[entryPoints]
[entryPoints.name]
address = ":8888"
[entryPoints.name.transport]
[entryPoints.name.transport.respondingTimeouts]
writeTimeout = 42## Static configuration
--entryPoints.name.address=:8888
--entryPoints.name.transport.respondingTimeouts.writeTimeout=42transport.respondingTimeouts.idleTimeout
Optional, Default=180s
idleTimeout is the maximum duration an idle (keep-alive) connection will remain idle before closing itself.
If zero, no timeout exists.
Can be provided in a format supported by time.ParseDuration or as raw values (digits).
If no units are provided, the value is parsed assuming seconds.
## Static configuration
entryPoints:
name:
address: ":8888"
transport:
respondingTimeouts:
idleTimeout: 42## Static configuration
[entryPoints]
[entryPoints.name]
address = ":8888"
[entryPoints.name.transport]
[entryPoints.name.transport.respondingTimeouts]
idleTimeout = 42## Static configuration
--entryPoints.name.address=:8888
--entryPoints.name.transport.respondingTimeouts.idleTimeout=42lifeCycle¶
Controls the behavior of Traefik during the shutdown phase.
lifeCycle.requestAcceptGraceTimeout
Optional, Default=0s
Duration to keep accepting requests prior to initiating the graceful termination period (as defined by the graceTimeOut option).
This option is meant to give downstream load-balancers sufficient time to take Traefik out of rotation.
Can be provided in a format supported by time.ParseDuration or as raw values (digits).
If no units are provided, the value is parsed assuming seconds. The zero duration disables the request accepting grace period, i.e., Traefik will immediately proceed to the grace period.
## Static configuration
entryPoints:
name:
address: ":8888"
transport:
lifeCycle:
requestAcceptGraceTimeout: 42## Static configuration
[entryPoints]
[entryPoints.name]
address = ":8888"
[entryPoints.name.transport]
[entryPoints.name.transport.lifeCycle]
requestAcceptGraceTimeout = 42## Static configuration
--entryPoints.name.address=:8888
--entryPoints.name.transport.lifeCycle.requestAcceptGraceTimeout=42lifeCycle.graceTimeOut
Optional, Default=10s
Duration to give active requests a chance to finish before Traefik stops.
Can be provided in a format supported by time.ParseDuration or as raw values (digits).
If no units are provided, the value is parsed assuming seconds.
In this time frame no new requests are accepted.
## Static configuration
entryPoints:
name:
address: ":8888"
transport:
lifeCycle:
graceTimeOut: 42## Static configuration
[entryPoints]
[entryPoints.name]
address = ":8888"
[entryPoints.name.transport]
[entryPoints.name.transport.lifeCycle]
graceTimeOut = 42## Static configuration
--entryPoints.name.address=:8888
--entryPoints.name.transport.lifeCycle.graceTimeOut=42keepAliveMaxRequests¶
Optional, Default=0
The maximum number of requests Traefik can handle before sending a Connection: Close header to the client (for HTTP2, Traefik sends a GOAWAY). Zero means no limit.
## Static configuration
entryPoints:
name:
address: ":8888"
transport:
keepAliveMaxRequests: 42## Static configuration
[entryPoints]
[entryPoints.name]
address = ":8888"
[entryPoints.name.transport]
keepAliveMaxRequests = 42## Static configuration
--entryPoints.name.address=:8888
--entryPoints.name.transport.keepAliveMaxRequests=42keepAliveMaxTime¶
Optional, Default=0s
The maximum duration Traefik can handle requests before sending a Connection: Close header to the client (for HTTP2, Traefik sends a GOAWAY). Zero means no limit.
## Static configuration
entryPoints:
name:
address: ":8888"
transport:
keepAliveMaxTime: 42s## Static configuration
[entryPoints]
[entryPoints.name]
address = ":8888"
[entryPoints.name.transport]
keepAliveMaxTime = 42s## Static configuration
--entryPoints.name.address=:8888
--entryPoints.name.transport.keepAliveMaxTime=42sProxyProtocol¶
Traefik supports PROXY protocol version 1 and 2.
If PROXY protocol header parsing is enabled for the entry point, this entry point can accept connections with or without PROXY protocol headers.
If the PROXY protocol header is passed, then the version is determined automatically.
proxyProtocol.trustedIPs
Enabling PROXY protocol with Trusted IPs.
## Static configuration
entryPoints:
web:
address: ":80"
proxyProtocol:
trustedIPs:
- "127.0.0.1/32"
- "192.168.1.7"## Static configuration
[entryPoints]
[entryPoints.web]
address = ":80"
[entryPoints.web.proxyProtocol]
trustedIPs = ["127.0.0.1/32", "192.168.1.7"]--entryPoints.web.address=:80
--entryPoints.web.proxyProtocol.trustedIPs=127.0.0.1/32,192.168.1.7IPs in trustedIPs only will lead to remote client address replacement: Declare load-balancer IPs or CIDR range here.
proxyProtocol.insecure
Insecure Mode (Testing Environment Only).
In a test environments, you can configure Traefik to trust every incoming connection.
Doing so, every remote client address will be replaced (trustedIPs won't have any effect)
## Static configuration
entryPoints:
web:
address: ":80"
proxyProtocol:
insecure: true## Static configuration
[entryPoints]
[entryPoints.web]
address = ":80"
[entryPoints.web.proxyProtocol]
insecure = true--entryPoints.web.address=:80
--entryPoints.web.proxyProtocol.insecureQueuing Traefik behind Another Load Balancer
When queuing Traefik behind another load-balancer, make sure to configure PROXY protocol on both sides. Not doing so could introduce a security risk in your system (enabling request forgery).
HTTP Options¶
This whole section is dedicated to options, keyed by entry point, that will apply only to HTTP routing.
Redirection¶
HTTPS redirection (80 to 443)
entryPoints:
web:
address: :80
http:
redirections:
entryPoint:
to: websecure
scheme: https
websecure:
address: :443[entryPoints.web]
address = ":80"
[entryPoints.web.http]
[entryPoints.web.http.redirections]
[entryPoints.web.http.redirections.entryPoint]
to = "websecure"
scheme = "https"
[entryPoints.websecure]
address = ":443"--entryPoints.web.address=:80
--entryPoints.web.http.redirections.entryPoint.to=websecure
--entryPoints.web.http.redirections.entryPoint.scheme=https
--entryPoints.websecure.address=:443entryPoint¶
This section is a convenience to enable (permanent) redirecting of all incoming requests on an entry point (e.g. port 80) to another entry point (e.g. port 443) or an explicit port (:443).
entryPoint.to
Required
The target element, it can be:
- an entry point name (ex:
websecure) - a port (
:443)
entryPoints:
foo:
# ...
http:
redirections:
entryPoint:
to: websecure[entryPoints.foo]
# ...
[entryPoints.foo.http.redirections]
[entryPoints.foo.http.redirections.entryPoint]
to = "websecure"--entryPoints.foo.http.redirections.entryPoint.to=websecureentryPoint.scheme
Optional, Default="https"
The redirection target scheme.
entryPoints:
foo:
# ...
http:
redirections:
entryPoint:
# ...
scheme: https[entryPoints.foo]
# ...
[entryPoints.foo.http.redirections]
[entryPoints.foo.http.redirections.entryPoint]
# ...
scheme = "https"--entryPoints.foo.http.redirections.entryPoint.scheme=httpsentryPoint.permanent
Optional, Default=true
To apply a permanent redirection.
entryPoints:
foo:
# ...
http:
redirections:
entryPoint:
# ...
permanent: true[entryPoints.foo]
# ...
[entryPoints.foo.http.redirections]
[entryPoints.foo.http.redirections.entryPoint]
# ...
permanent = true--entryPoints.foo.http.redirections.entrypoint.permanent=trueentryPoint.priority
Optional, Default=MaxInt-1
Priority of the generated router.
entryPoints:
foo:
# ...
http:
redirections:
entryPoint:
# ...
priority: 10[entryPoints.foo]
# ...
[entryPoints.foo.http.redirections]
[entryPoints.foo.http.redirections.entryPoint]
# ...
priority = 10--entryPoints.foo.http.redirections.entrypoint.priority=10EncodeQuerySemicolons¶
Optional, Default=false
The encodeQuerySemicolons option allows to enable query semicolons encoding.
One could use this option to avoid non-encoded semicolons to be interpreted as query parameter separators by Traefik.
When using this option, the non-encoded semicolons characters in query will be transmitted encoded to the backend.
entryPoints:
websecure:
address: ':443'
http:
encodeQuerySemicolons: true[entryPoints.websecure]
address = ":443"
[entryPoints.websecure.http]
encodeQuerySemicolons = true--entryPoints.websecure.address=:443
--entryPoints.websecure.http.encodequerysemicolons=trueExamples¶
| EncodeQuerySemicolons | Request Query | Resulting Request Query |
|---|---|---|
| false | foo=bar;baz=bar | foo=bar&baz=bar |
| true | foo=bar;baz=bar | foo=bar%3Bbaz=bar |
| false | foo=bar&baz=bar;foo | foo=bar&baz=bar&foo |
| true | foo=bar&baz=bar;foo | foo=bar&baz=bar%3Bfoo |
Middlewares¶
The list of middlewares that are prepended by default to the list of middlewares of each router associated to the named entry point.
entryPoints:
websecure:
address: ':443'
http:
middlewares:
- auth@file
- strip@file[entryPoints.websecure]
address = ":443"
[entryPoints.websecure.http]
middlewares = ["auth@file", "strip@file"]--entryPoints.websecure.address=:443
--entryPoints.websecure.http.middlewares=auth@file,strip@fileTLS¶
This section is about the default TLS configuration applied to all routers associated with the named entry point.
If a TLS section (i.e. any of its fields) is user-defined, then the default configuration does not apply at all.
The TLS section is the same as the TLS section on HTTP routers.
entryPoints:
websecure:
address: ':443'
http:
tls:
options: foobar
certResolver: leresolver
domains:
- main: example.com
sans:
- foo.example.com
- bar.example.com
- main: test.com
sans:
- foo.test.com
- bar.test.com[entryPoints.websecure]
address = ":443"
[entryPoints.websecure.http.tls]
options = "foobar"
certResolver = "leresolver"
[[entryPoints.websecure.http.tls.domains]]
main = "example.com"
sans = ["foo.example.com", "bar.example.com"]
[[entryPoints.websecure.http.tls.domains]]
main = "test.com"
sans = ["foo.test.com", "bar.test.com"]--entryPoints.websecure.address=:443
--entryPoints.websecure.http.tls.options=foobar
--entryPoints.websecure.http.tls.certResolver=leresolver
--entryPoints.websecure.http.tls.domains[0].main=example.com
--entryPoints.websecure.http.tls.domains[0].sans=foo.example.com,bar.example.com
--entryPoints.websecure.http.tls.domains[1].main=test.com
--entryPoints.websecure.http.tls.domains[1].sans=foo.test.com,bar.test.comLet's Encrypt
entryPoints:
websecure:
address: ':443'
http:
tls:
certResolver: leresolver[entryPoints.websecure]
address = ":443"
[entryPoints.websecure.http.tls]
certResolver = "leresolver"--entryPoints.websecure.address=:443
--entryPoints.websecure.http.tls.certResolver=leresolverUDP Options¶
This whole section is dedicated to options, keyed by entry point, that will apply only to UDP routing.
Timeout¶
Optional, Default=3s
Timeout defines how long to wait on an idle session before releasing the related resources. The Timeout value must be greater than zero.
entryPoints:
foo:
address: ':8000/udp'
udp:
timeout: 10s[entryPoints.foo]
address = ":8000/udp"
[entryPoints.foo.udp]
timeout = "10s"--entryPoints.foo.address=:8000/udp
--entryPoints.foo.udp.timeout=10sUsing Traefik for Business Applications?
If you are using Traefik in your organization, consider our enterprise-grade solutions:
- API Management
Explore // Watch Demo Video - API Gateway
Explore // Watch Demo Video - Ingress Controller
Kubernetes // Docker Swarm
These tools help businesses discover, deploy, secure, and manage microservices and APIs easily, at scale, across any environment.